How Vendor Access Practices Led to Data Breaches at LA Manufacturers in 2025
In 2025, LA's manufacturing sector faced a dramatic increase in cyberattacks — many stemming from risky access practices granted to third-party vendors. Here's what happened and what to do.
In 2025, Los Angeles's manufacturing sector faced a dramatic increase in cyberattacks — many stemming not from their own internal gaps, but from risky access practices granted to third-party vendors.
Vendor Access: The Hidden Risk
When manufacturers grant remote access to service providers, software vendors, and supply chain partners, they open privileged doors to their digital infrastructure. In LA, the biggest breaches this year were frequently traced back to a handful of high-risk vendor behaviors:
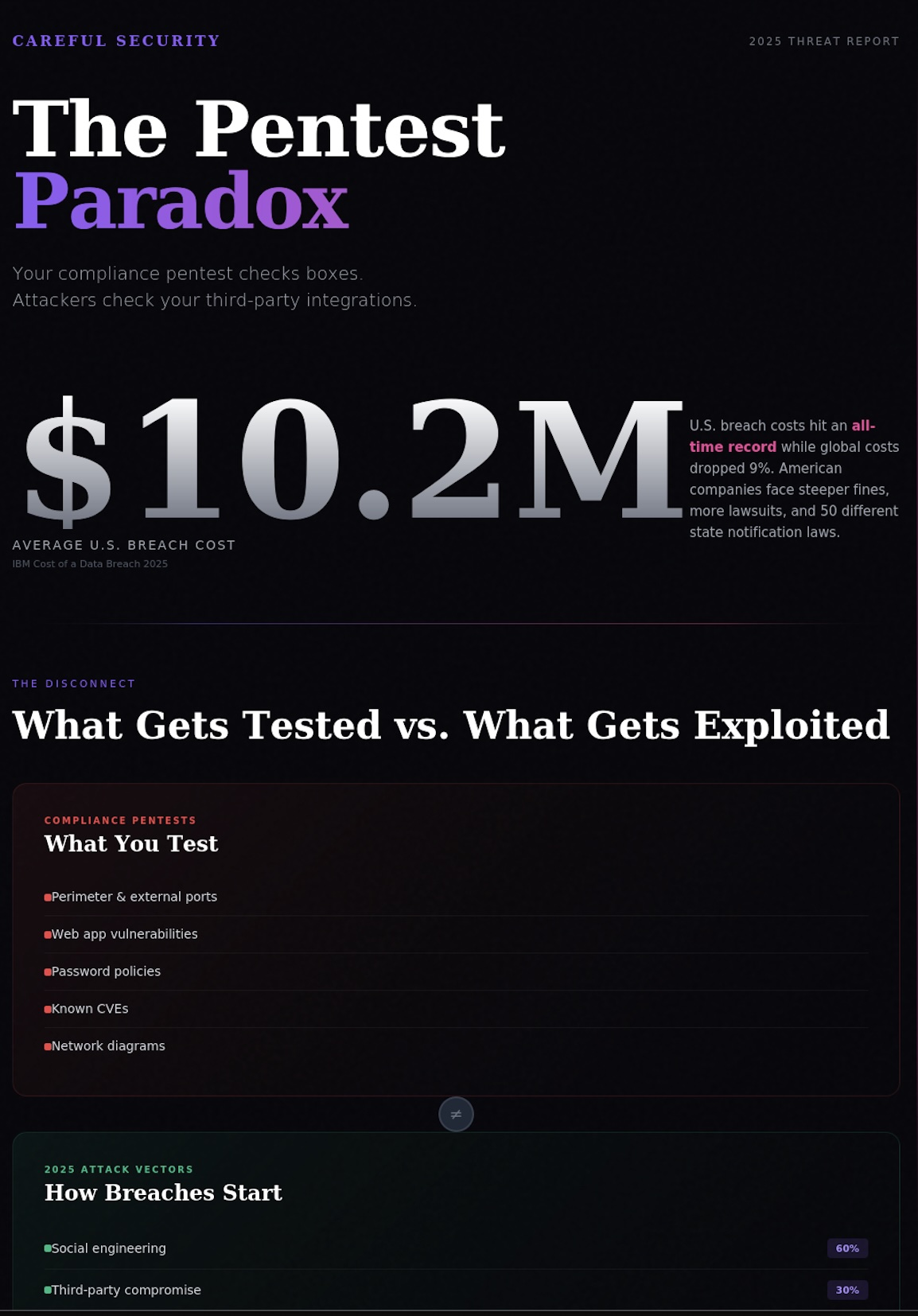
- •Excessive and unchecked access privileges — factories often allowed vendors full administrative or unrestricted access, lacking segmentation or role-based controls. 35% of manufacturing breaches nationwide in 2025 directly stemmed from these 'open gate' permissions
- •No security vetting or periodic review — more than half of LA manufacturers failed to assess the cybersecurity posture of vendors before granting network access
- •Poor visibility into vendor network access — 43% had no comprehensive inventory of which vendors had ongoing access
- •Insecure remote access tools — many breaches exploited unpatched remote desktop utilities, exposed IoT devices with public IPs, or poorly configured VPNs
- •Lack of privileged-access management — without enforcing least privilege, some vendors could perform unauthorized actions
Real-World LA Incidents
Los Angeles Cold Storage was breached in February 2025 via ransomware, with reports citing vulnerabilities linked to remote third-party access. The incident highlighted how poorly managed remote connectivity exposed payroll and operational data to threat actors.
Lessons for LA Manufacturers
- •Vetting and monitoring — consistently vet vendor security before on-boarding and require regular documented reviews
- •Inventory and segmentation — maintain detailed inventories of vendor access and segment network permissions
- •Update and secure remote access — replace outdated remote access tools, enforce MFA, and close public-facing network holes
For Los Angeles manufacturers, mitigating supply chain cyber risk means being relentless about vendor security — treating every third-party connection as a potential attack vector.
Questions about this article? Book a free 30-minute consultation and talk directly with a senior practitioner.
Book Free Consultation →